In this comprehensive guide, I will walk you through exactly how to backup storage accounts in Azure. I will explain the native tools, the managed Azure Backup service, and the strategies I personally recommend to ensure your data remains bulletproof against ransomware, accidental deletions, and corruption.
Table of Contents
- How to Backup Storage Account in Azure
- Disaster Recovery: Object Replication
How to Backup Storage Account in Azure
The Critical Distinction: Redundancy vs. Backup
Before we dive into the “how-to,” I need to clarify the “why.” When you create a Storage Account in Azure, you select a replication strategy—typically Locally-Redundant Storage (LRS), Zone-Redundant Storage (ZRS), or Geo-Redundant Storage (GRS).
Here is the hard truth: Replication protects you from hardware failures; Backup protects you from logic failures and human error.
If a disgruntled employee performs a hard delete on a container, or if a ransomware script encrypts your files, that deletion or corruption is instantly replicated to all redundant copies. If you have GRS (Geo-Redundant Storage) enabled between East US and West US, the corruption is faithfully copied to the West US region.
To truly protect your storage account, you need a strategy that allows for point-in-time recovery.
Layer 1: Native Data Protection Features
In my experience, the first line of defense is often the most effective for quick recovery. Azure Storage offers several “Data Protection” features that operate at the storage account level. These are not “backups” in the traditional sense of a secondary copy, but they are essential for operational recovery.
Soft Delete for Blobs and Containers
I always recommend enabling Soft Delete immediately upon creating a storage account. Soft delete acts like a “Recycle Bin” for your storage. When you turn this on, any blob or container that is deleted is not actually removed; it is marked as soft-deleted and held for a retention period you specify (between 1 and 365 days).
During this window, I can restore the data to its state prior to deletion. For most US-based compliance standards, I typically recommend a retention period of at least 14 to 30 days.
Blob Versioning
Versioning is distinct from Soft Delete. When I enable versioning, Azure automatically maintains the history of a blob. Every time a blob is overwritten, a “version” is created.
Table: Comparison of Native Protection Features
| Feature | Primary Use Case | Protection Type |
| Soft Delete | Accidental Deletion | Recover deleted items for $X$ days. |
| Versioning | Overwrites/Corruption | Restore a specific previous state of a file. |
| Change Feed | Auditing | Logs all changes (creation, modification, deletion). |
| Point-in-Time Restore | Mass Restoration | Roll back the entire container to a specific timestamp. |
Layer 2: Azure Backup for Blobs (Operational Backup)
While native features are great, managing them at scale can be tedious. This is where Azure Backup comes into play. Microsoft has introduced a managed solution known as Operational Backup for Blobs.
Instead of sending your data to a separate “vault” (which transfers data and incurs high bandwidth costs), Operational Backup is a local backup solution. It orchestrates the native capabilities I mentioned above (Soft Delete, Versioning, and Point-in-Time Restore) but manages them through a centralized Backup Policy.
How I Configure Operational Backup
When I set this up for clients, I don’t go to the Storage Account blade first. I go to the Backup Center.
- Backup Vault Creation: I create a Backup Vault (not to be confused with a Recovery Services Vault).
- Policy Definition: I define a backup policy. For example, I might set a policy that enforces retention of data for 30 days.
- Assignment: I assign this policy to the specific Storage Accounts.
The beauty of this approach is that the data doesn’t leave the storage account, meaning the backups are incredibly fast and cost-effective.
If your organization uses Azure Files (the SMB protocol service), the backup methodology is slightly different compared to Blobs. For Azure Files, Azure Backup uses the snapshot capability.
The Snapshot Mechanism
When I configure backup for Azure File Shares, the service takes scheduled snapshots of the file share. These snapshots are incremental. If I have a 1TB file share but only change 5GB of data today, the snapshot will only consume storage equivalent to that 5GB change.
Configuring the Recovery Services Vault
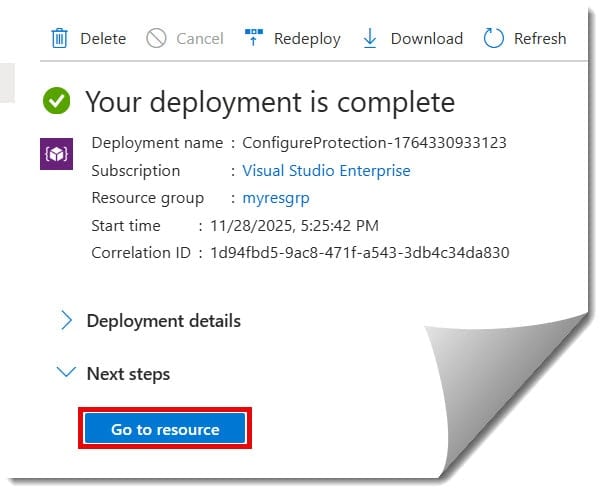
Unlike Blobs, Azure Files are backed up using a Recovery Services Vault. Here is the high-level workflow I follow:
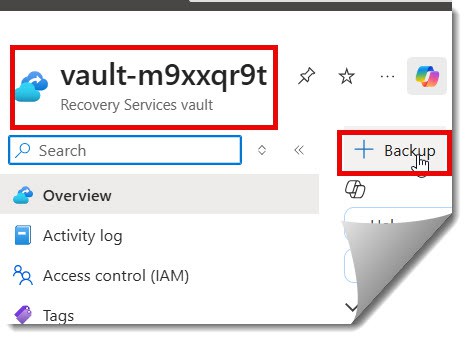
- Navigate to the Recovery Services Vault in the Azure Portal.
- Select + Backup.
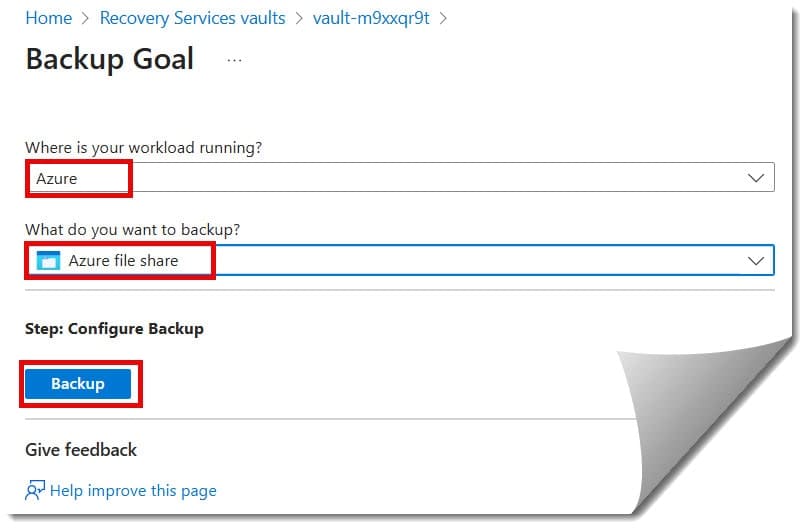
- Choose Azure as the workload and Azure File Share as the resource type.
- Select the Storage Account and the specific File Share to protect.
- Define the Backup Policy. Check out the screenshots below for the complete steps.
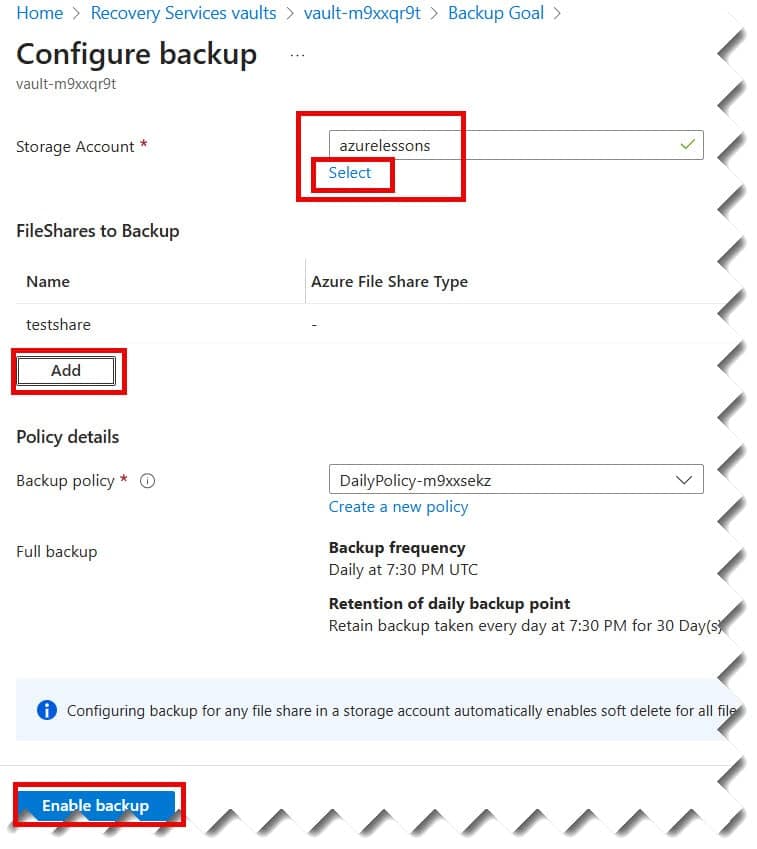
Pro Tip: For US enterprise clients, I usually configure a “GFS” policy.
- Daily backups: Retained for 30 days.
- Weekly backups: Retained for 12 weeks.
- Monthly backups: Retained for 60 months (5 years) to satisfy tax and legal audits.
Layer 4: Immutable Storage for Legal Holds
In the United States, industries like healthcare (HIPAA) and finance (SEC Rule 17a-4) have strict requirements regarding data immutability. They require Write-Once-Read-Many (WORM) storage.
Azure Storage supports this via Immutable Storage Policies.
Time-Based Retention
I can apply a policy that locks data for a specific duration. If I set a 7-year retention policy on a container containing financial records, no one—not even the account administrator or Microsoft support—can delete or modify those files until the timer expires.
Legal Hold
Alternatively, I can place a “Legal Hold” tag. This is indefinite. The data is immutable until I explicitly remove the legal hold tag. This is essential when an organization is involved in active litigation.
Disaster Recovery: Object Replication
We discussed earlier that redundancy is not backup. However, redundancy is still vital for Disaster Recovery (DR). What happens if the entire ‘East US 2’ region goes offline due to a catastrophic natural disaster?
For this, I utilize Object Replication.
Object Replication allows me to asynchronously copy block blobs from a source storage account in one region to a destination account in another region. Unlike standard GRS (which is a black box managed by Microsoft), Object Replication gives me granular control.
- Granularity: I can choose to replicate only specific containers.
- Filtering: I can replicate specific blob versions.
- Architecture: I typically set up the primary account in
East USand the replication target inWest USorCentral US.
This ensures that even if the primary region is vaporized, I have a secondary, accessible copy of the data that I control.
Step-by-Step Strategy for a Secure Storage Account
If you are setting up a new Storage Account today, here is the exact checklist I recommend you follow to ensure full “backup” coverage.
1. Enable Data Protection Immediately
Do not wait. As soon as the resource is provisioned, go to the “Data Protection” blade. Enable Soft Delete for Blobs (7+ days), Soft Delete for Containers (7+ days), and enable Versioning.
2. Configure a Backup Vault
Go to the Backup Center in Azure. Create a Backup Policy that aligns with your company’s RPO (Recovery Point Objective) and RTO (Recovery Time Objective). Apply this policy to your storage account. This ensures that even if someone disables the soft delete settings on the account manually, the backup policy helps govern the data lifecycle.
3. Lock the Resources
I always apply an Azure Resource Lock (specifically a CanNotDelete lock) on the Storage Account itself. This prevents an administrator from accidentally deleting the entire storage account resource from the Azure Portal, which is a surprisingly common disaster scenario.
4. Monitor and Alert
Backups are useless if they are failing. I set up alerts using Azure Monitor. I want an email notification sent to the IT Ops team immediately if a backup job fails or if the “delete” volume on a storage account spikes unexpectedly (a potential indicator of a ransomware attack in progress).
Cost Considerations for the US Market
When architecting these solutions, cost is always a factor. Backup in Azure is cost-effective, but it is not free.
- Snapshot Costs: You pay for the storage consumed by snapshots. If your data changes rapidly (high churn), your snapshot costs will equal or exceed your production storage costs.
- Operational Backup: There is a small management fee per protected instance, plus the cost of the additional storage used by soft delete and versioning.
- Archive Tier: For long-term retention (e.g., keeping data for 7 years), do not keep snapshots in the Hot tier. I recommend moving older data to the Archive Tier. The cost for Archive storage in the US regions is a fraction of a cent per GB, making it ideal for “write and forget” backups.
Conclusion
Backing up a storage account in Azure is not a single “click-button” operation; it is a layered strategy. It requires a combination of native protection (Soft Delete), managed services (Azure Backup), and architectural decisions (Replication and Immutability).
By implementing the layers discussed in this guide—Operational Backup, Snapshots, and Resource Locks—you transform your Azure Storage from a simple data bucket into a resilient, enterprise-grade vault.
Take a moment today to audit your current storage accounts. If you don’t see “Soft Delete” enabled, that is your first action item.
You may also like the following articles:
- How to Connect to Azure Storage Account
- How to Secure Azure Storage Account
- How to get storage account key in Azure

I am Rajkishore, and I am a Microsoft Certified IT Consultant. I have over 14 years of experience in Microsoft Azure and AWS, with good experience in Azure Functions, Storage, Virtual Machines, Logic Apps, PowerShell Commands, CLI Commands, Machine Learning, AI, Azure Cognitive Services, DevOps, etc. Not only that, I do have good real-time experience in designing and developing cloud-native data integrations on Azure or AWS, etc. I hope you will learn from these practical Azure tutorials. Read more.

