In this comprehensive article, I will walk you through the professional steps for adding and managing devices within the Microsoft Entra admin center.
Table of Contents
- How To Add Device In Microsoft Entra Admin Center
How To Add Device In Microsoft Entra Admin Center
When a device is added to Microsoft Entra, it allows you to:
- Enforce Conditional Access: Ensure only “Compliant” devices can access Outlook or SharePoint.
- Enable Single Sign-On (SSO): Users sign in once to the device and get seamless access to all corporate apps.
- Simplify Remote Work: Perfect for the modern hybrid workforce in hubs .
Understanding the Three Types of Device Identities
Before we jump into the admin center, we must clarify how a device is added. In Microsoft Entra, “adding” a device isn’t always a manual upload by an admin; it’s often a registration triggered by the user or an automated system.
1. Entra Registered Devices
Typically used for Bring Your Own Device (BYOD) scenarios. These are personal devices (Windows, iOS, Android, macOS) used by employees to access corporate resources.
- Ownership: User-owned.
- Authentication: Uses a local account but registers with Entra for cloud access.
2. Entra Joined Devices
These are strictly corporate-owned devices. They are joined only to Microsoft Entra ID and do not require an on-premises Active Directory.
- Ownership: Organization-owned.
- Authentication: Users sign in with their corporate Entra ID account (e.g.,
name@company.com).
3. Hybrid Entra Joined Devices
For established firms that still rely on an on-premises Active Directory but want cloud benefits. These devices are “joined” to the local AD and “registered” in the cloud.
Accessing the Microsoft Entra Admin Center
To begin, you need the right permissions. I recommend using the Global Administrator or Cloud Device Administrator role for these tasks.
- Navigate to the Microsoft Entra admin center.
- Sign in with your administrative credentials.
- On the left-hand sidebar, expand the Identity menu.
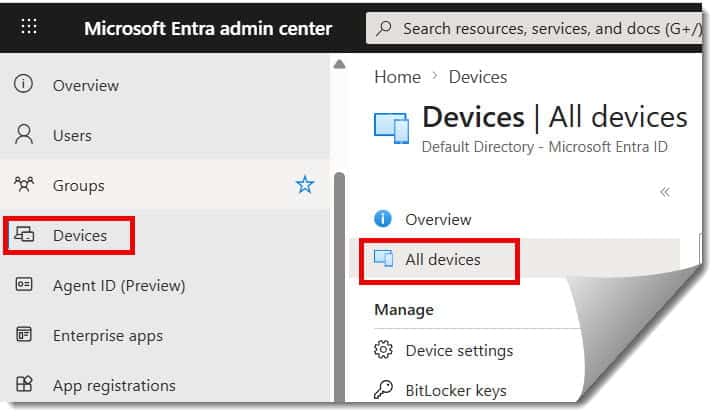
- Select Devices and then click on All devices. Check out the screenshot below for your reference.
Check out How To Access Microsoft Entra Admin Center
Step-by-Step Tutorial: How a Device is Added to the Portal
In the Entra admin center, “adding” a device usually involves configuring the settings that allow devices to join, or manually importing hardware identifiers for automated deployment.
Phase 1: Configuring Device Settings
Before a user can add their device, you must permit the action in the portal.
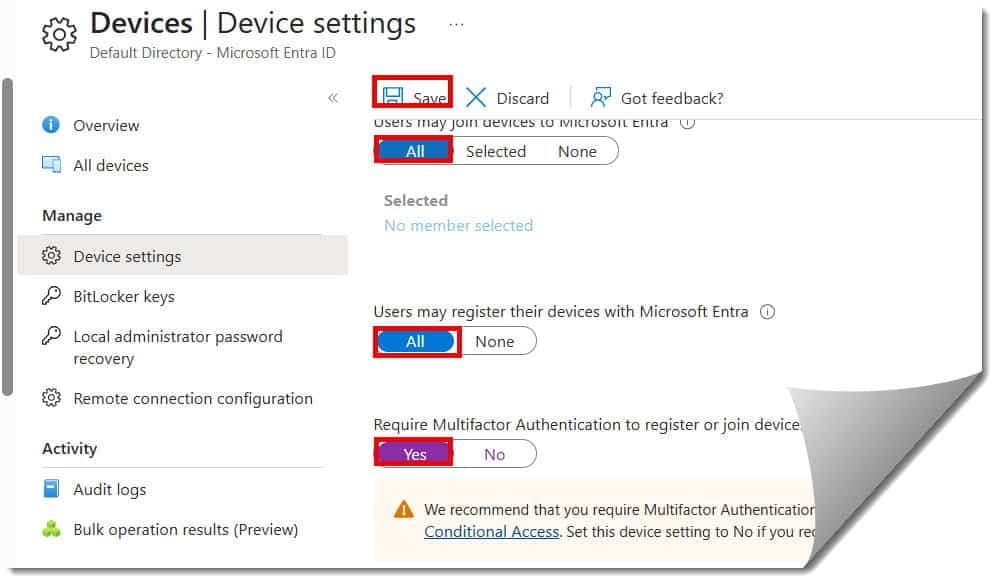
- Go to: Devices > Device settings.
- Users may join devices to Microsoft Entra ID: Set this to “All” or “Selected” (highly recommended for security).
- Additional local administrators: Here, you can designate IT staff with local admin rights on all joined devices.
- Require Multi-Factor Authentication (MFA): Set this to “Yes.” This is a security “must-have” in the USA to prevent rogue devices from joining your tenant. Check out the screenshot below for your reference.
Phase 2: Adding Windows Devices via “Work or School”
For most Windows 10 or 11 users, the “adding” happens on the client side, which then populates the Entra portal.
- On the local PC, go to Settings > Accounts > Access work or school.
- Click Connect.
- To Register (BYOD): Enter the email address and sign in.
- To Join (Corporate): Click the link at the bottom that says “Join this device to Microsoft Entra ID”.
- Once the user completes the MFA prompt, the device will appear in your All devices list in the admin center.
Managing Bulk Additions with Windows Autopilot
If you are a sysadmin for a massive logistics company, you don’t want to manually join 500 laptops. Instead, we use Windows Autopilot, which allows you to “pre-add” devices using a hardware hash.
Importing Hardware Hashes
- Obtain the CSV file containing the hardware hashes from your hardware vendor (e.g., Dell or HP).
- In the Entra admin center (or Intune/Microsoft Endpoint Manager), navigate to Devices > Windows > Windows enrollment.
- Select Devices under the Windows Autopilot Deployment Program.
- Click Import and upload your CSV.
- Once imported, these devices are “pre-added.” When the employee unboxes the laptop and connects to Wi-Fi, it will automatically join your Entra tenant.
Device Management Comparison Table
| Feature | Entra Registered | Entra Joined | Hybrid Joined |
| Typical User | Contractor / BYOD | Modern Cloud Worker | Legacy Enterprise |
| Primary Login | Personal (MSA/Local) | Corporate (Entra ID) | AD Domain Account |
| MFA Support | Yes | Yes | Yes |
| GPO Support | No | No (Uses MDM/Intune) | Yes (Local AD) |
| USA Use Case | Small biz in Portland | Tech startup in Austin | Bank in NYC |
Troubleshooting: Why a Device Isn’t Appearing
Even with a perfect setup, you might run into issues where a device simply won’t show up in the “All devices” list. Here is my professional troubleshooting checklist:
1. Check the Quota
By default, Microsoft Entra ID limits the number of devices a single user can join.
- The Fix: Go to Devices > Device settings and check the Maximum number of devices per user. If it’s set to 20 and your power user is on their 21st gadget, the join will fail.
2. Verify DNS and Connectivity
If a device in a satellite office can’t reach the Microsoft login endpoints, the registration will fail.
- The Fix: Ensure your firewall allows traffic to
enterprise registration.windows.netandlogin.microsoftonline.com.
3. Review the Audit Logs
When in doubt, let the logs tell the story.
- The Fix: In the Entra admin center, go to Identity > Monitoring & health > Audit logs. Filter by “Device” to see exactly why a registration request was rejected.
Conclusion
Adding a device to the Microsoft Entra admin center is the first step toward a Zero Trust security model. By moving away from simple passwords and toward “Device Identity,” you ensure that your corporate data is only accessible by hardware that you trust and manage.
You may also like the following articles:
- How To Restrict Access To Microsoft Entra Admin Center
- Disable Device In Azure AD
- Backup/Restore to URL device error
- Microsoft Entra ID Tutorial For Beginners

I am Rajkishore, and I am a Microsoft Certified IT Consultant. I have over 14 years of experience in Microsoft Azure and AWS, with good experience in Azure Functions, Storage, Virtual Machines, Logic Apps, PowerShell Commands, CLI Commands, Machine Learning, AI, Azure Cognitive Services, DevOps, etc. Not only that, I do have good real-time experience in designing and developing cloud-native data integrations on Azure or AWS, etc. I hope you will learn from these practical Azure tutorials. Read more.

